When you remove a team member from a Deepgram project, any API keys they created are automatically disabled. If those keys are in use in production, this causes an outage.
This guide explains how to safely offboard team members without disrupting your services.
In Deepgram, every API key belongs to a project but is created by a specific user. This distinction matters:
When you remove a user from a project, all API keys they created are automatically disabled — even if those keys are actively used in production. This security feature ensures former team members can’t retain API access, but it means you need to plan ahead when offboarding users.
This ownership model provides:
A key’s effective permissions are also limited by its creator’s role. If a user with the Owner role creates an Owner-scoped key and is later demoted to Admin, the key loses its Owner permissions too. This is another reason to create production keys with a stable service account rather than an individual whose role may change.
When you attempt to remove a team member in Console, you’ll see a warning if they have active API keys.
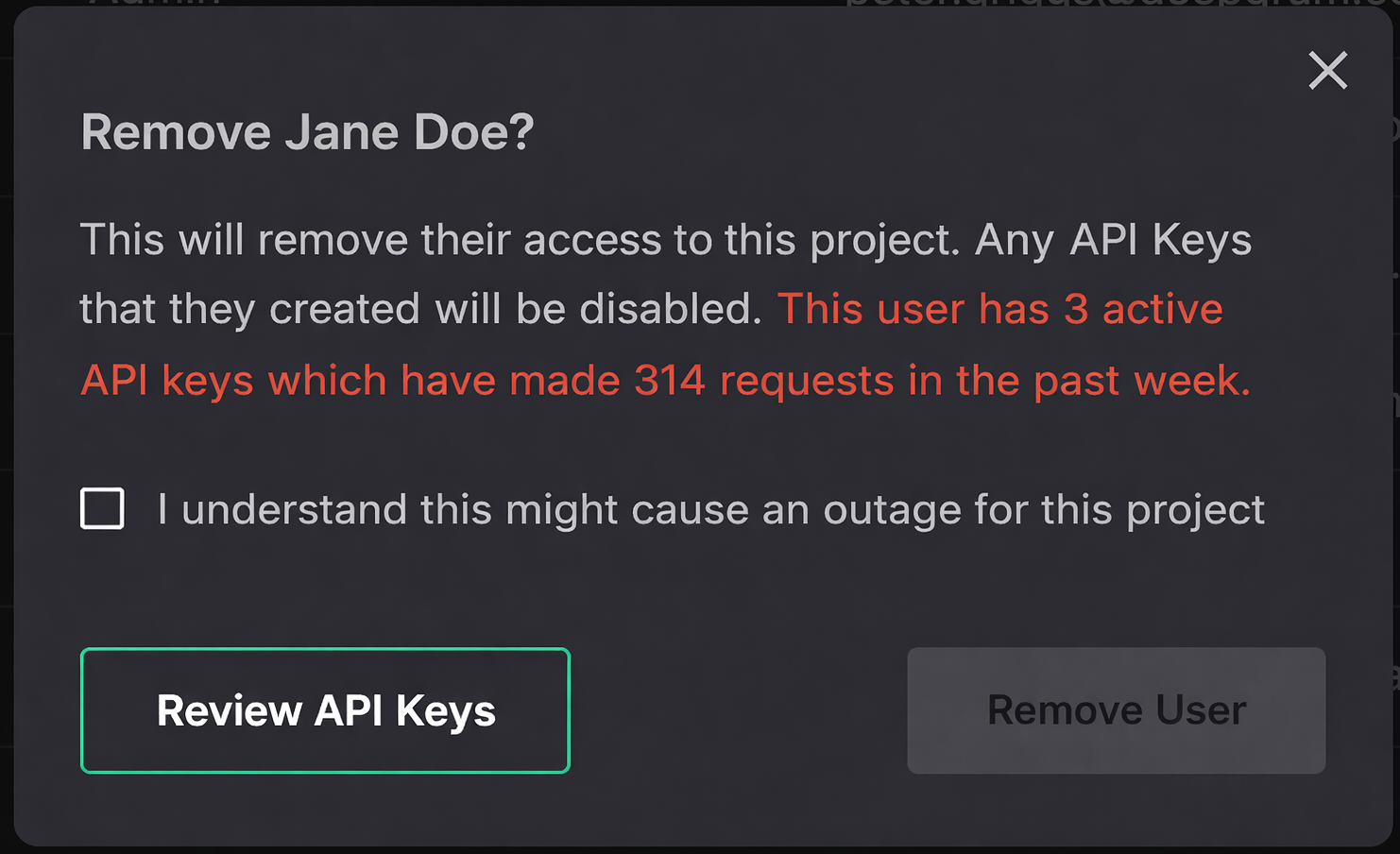
The warning shows:
If you see this warning, do not proceed until you’ve completed the migration steps below.
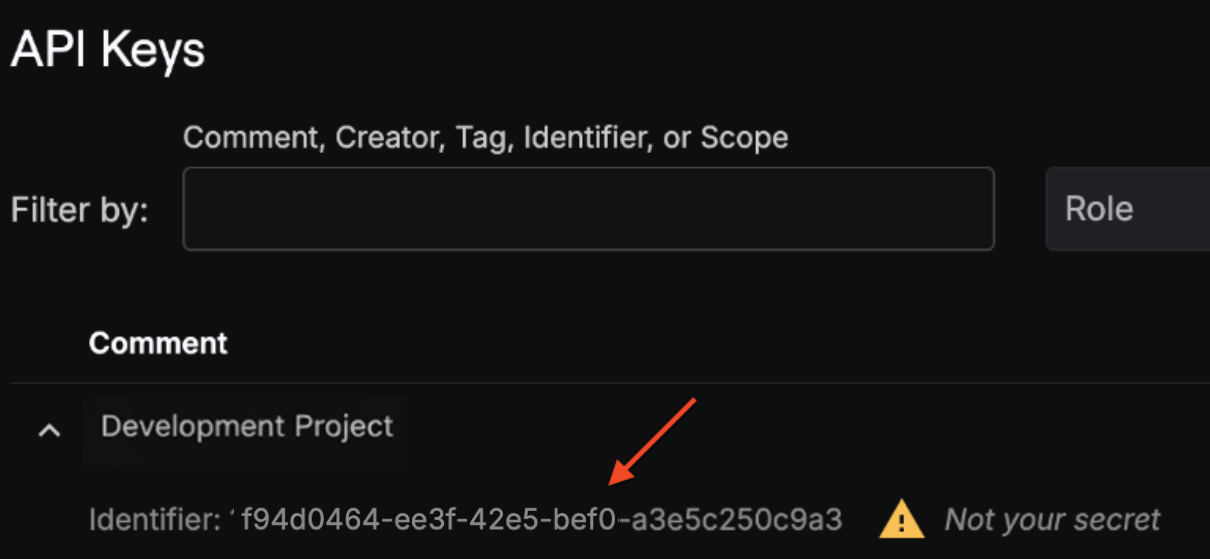
The removal dialog already tells you how many active keys the user has and their recent request count. To see the details:
Note the key names (comments) and Key IDs. You’ll need these to:
If the user created keys with descriptive names (e.g., “Production - Main App”, “Staging”), that gives you a clue about where they’re used. If names are generic, check Usage in Console to see request volume and patterns for each key, or ask your team which systems use which keys.
For each active key that needs to be replaced:
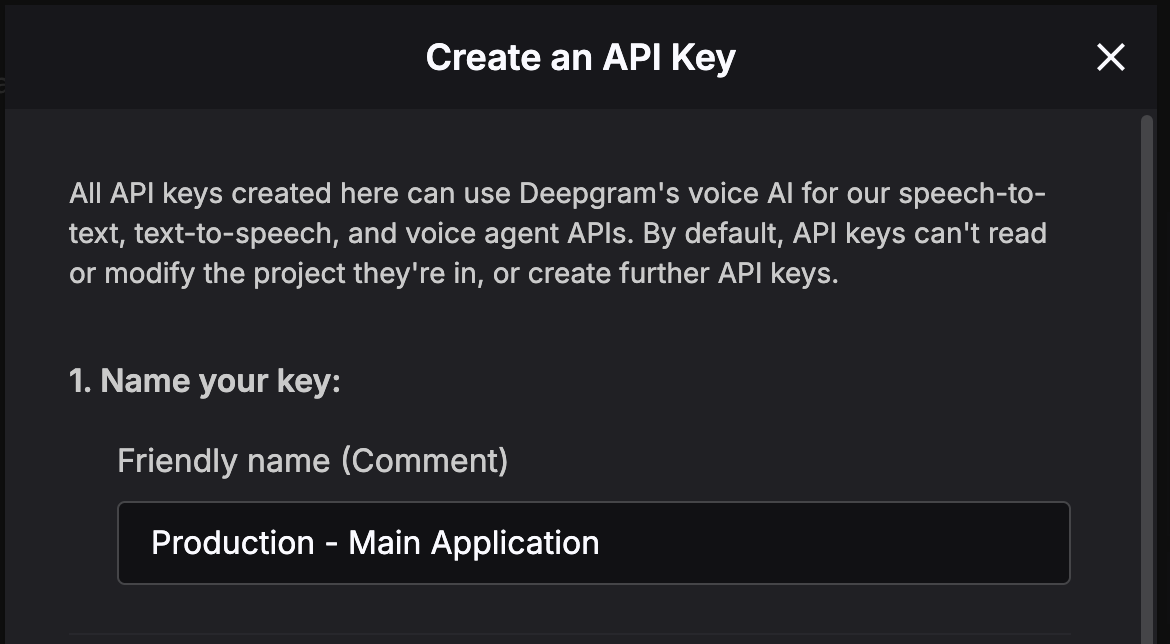
Copy and securely store the secret immediately — it won’t be shown again.
To learn more about creating API keys, see Creating API Keys. To learn more about roles, see Working with Roles.
Create production API keys using a designated service account (for example, engineering@yourcompany.com) rather than an individual user.
Service accounts are less likely to be removed during normal team changes, reducing the need for urgent key rotation.
Replace the old API key secret with the new one everywhere it’s used:
Deploy these changes to all environments before proceeding.
Before removing the user, confirm that traffic has moved to the new keys:
When is it safe to proceed?
Wait at least one full week before removing the user to ensure no background jobs or low-frequency systems are still using the old key.
Once you’ve confirmed the old keys have no active usage:
The user will lose access immediately, and all their API keys will be disabled.
You can still complete this process — you don’t need the departing user’s involvement. The key migration is done entirely by remaining team members with appropriate permissions.
If the person you’re removing is the only Owner of the project:
If the owner is completely unavailable, contact Deepgram Support for assistance.
If you must remove the user before completing migration (e.g., a security incident), understand that:
In this case, prioritize creating new keys and updating your most critical systems first.
engineering@company.com.production, staging). This makes migrations quick when needed.Questions? If you need help with this process or have questions about API key management, contact Deepgram Support.